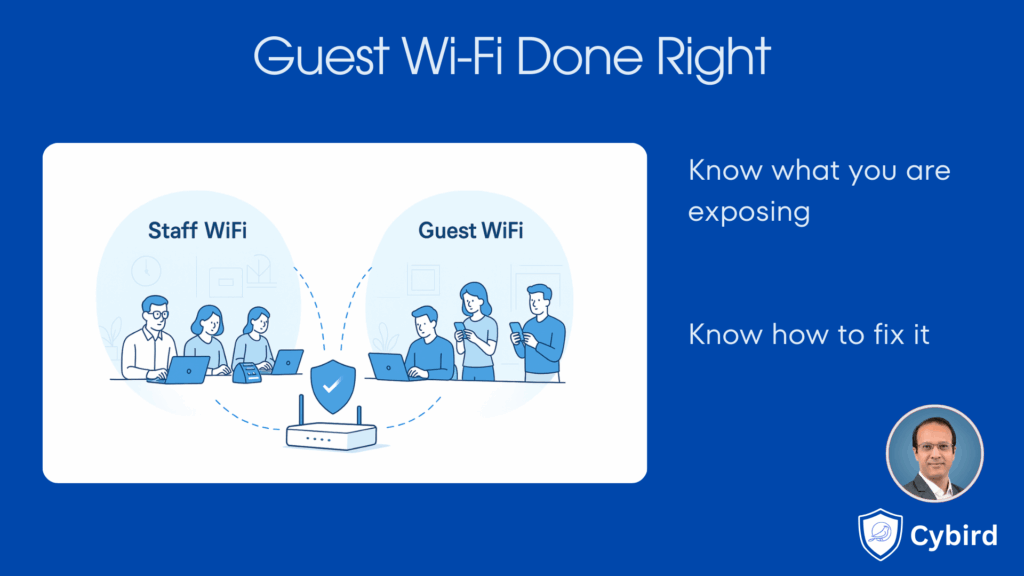
Offering free Wi-Fi to customers, partners and visitors is almost expected today. Cafes, clinics, coworking spaces and even small offices regularly share their Wi-Fi details so people can get online while they wait or work.
Done correctly, guest Wi-Fi is a nice touch that improves experience and keeps people productive.
Done incorrectly, it can quietly expose your business to malware, data leaks and outages.
This guide explains how small and midsize businesses can offer guest Wi-Fi in a way that keeps everyone happy while protecting the core business network. It is written for both SMB owners and MSPs who manage networks for them.

Why guest Wi-Fi is different from your staff Wi-Fi
Every device that joins your network is like a temporary visitor to your office. It can:
- Talk to other devices on the same network
- See shared folders and printers, if they are not locked down
- Try to reach your router, cameras, NAS boxes and point of sale systems
When the device belongs to an employee laptop that you manage, this risk is at least somewhat under control. You may have antivirus, patching and policies in place.
A guest device is different:
- You do not manage its security
- You do not control which apps are installed
- You do not know whether it is already infected
If you put guest devices on the same network as staff PCs, servers and internal systems, you are effectively trusting every visitor with the inside of your office network.
That is the core problem with guest Wi-Fi that is not done right.
Where guest Wi-Fi goes wrong in real life
Here are a few common patterns we see in small businesses.
One Wi-Fi for everything
There is a single Wi-Fi name and password for the entire office. Staff, guests, printers, cameras, smart TVs, even the POS tablet all connect to it.
Risks:
- A malware infected phone joins and starts scanning other devices
- A curious or bored guest opens the network browser and sees shared folders
- A contractor accidentally discovers your NAS backup share
All of this can happen without any hacking skills. Often it is simply a combination of infected devices and weak internal protections.
Guests can see internal resources
Some routers are configured so that any device on Wi-Fi can reach any IP address on the local network. Even if you have a separate guest SSID, if there is no isolation, guests can still:
- Ping or port scan your servers
- Reach printer admin pages
- Try default passwords on cameras or NAS devices
Guests ruin performance for everyone
Guest networks are sometimes left unlimited. One visitor starts a large software update or cloud backup. Suddenly:
- Video calls stutter
- Payment terminals slow down
- Cloud apps feel sluggish
From the business side it feels like “the internet is down” when it is really just overloaded.
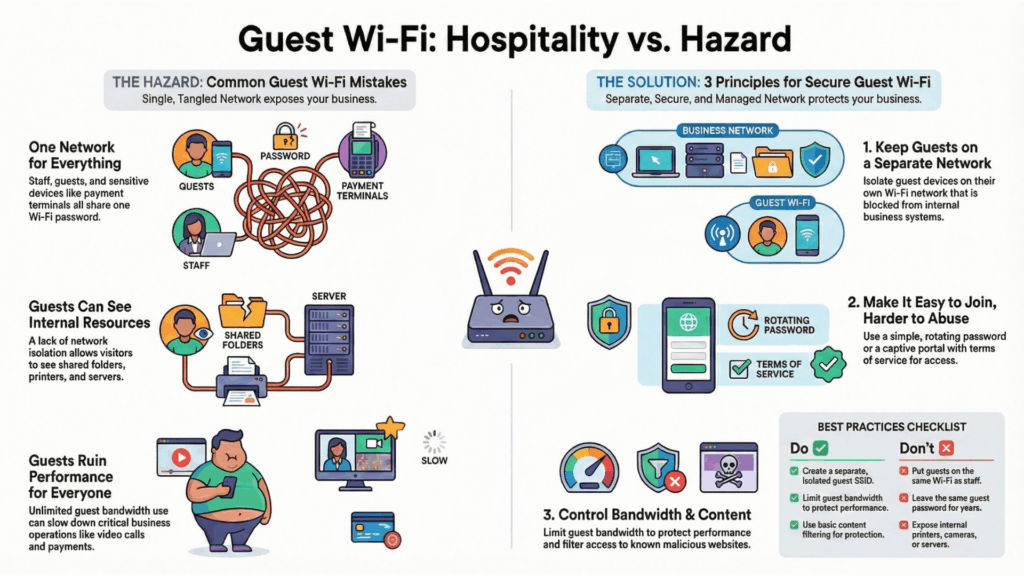
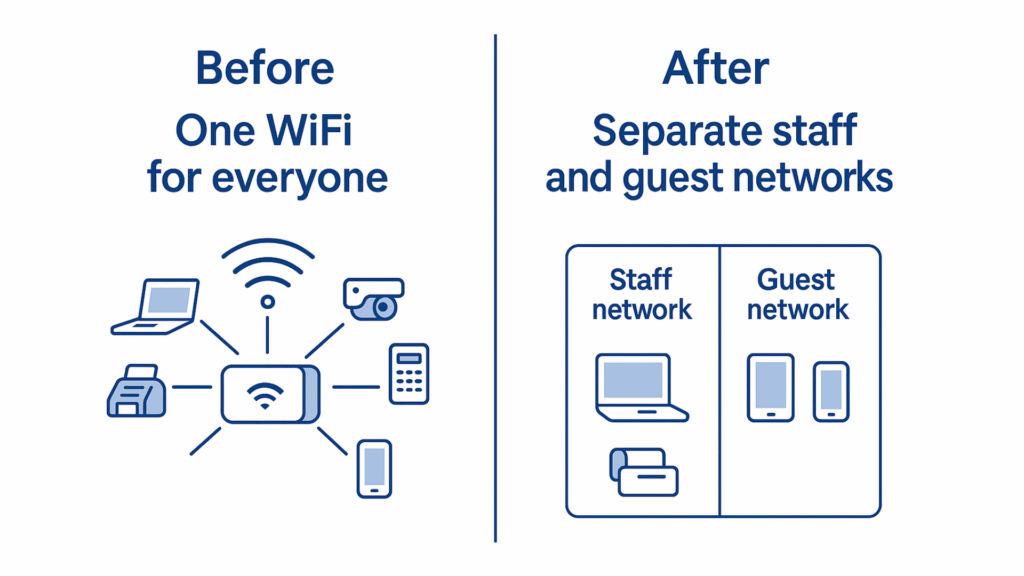
Principle 1: Keep guests on a separate network
The single most important rule of guest Wi-Fi is this:
Guest devices should never sit on the same network segment as your corporate devices.
In practical terms this means:
- A separate Wi-Fi name for guests, for example “CompanyName Guest”
- That guest Wi-Fi is mapped to its own internal network, separate from staff
- Rules that block guests from reaching internal IP ranges and devices
Technical people call this segmentation or network isolation. For SMBs, you can think of it as putting a locked glass wall between guests and your business systems. They can see the internet, but they cannot step into your internal space.
What “isolated guest network” should mean
A properly isolated guest SSID should:
- Allow browsing the internet
- Block access to your internal IP ranges for example 192.168.10.x where staff devices live
- Prevent guests from talking to each other peer to peer isolation, so one infected phone cannot attack another guest
- Hide internal services like file shares, printers and camera consoles
With the right router or security solution, this is usually a simple configuration choice, not a complex project.
Principle 2: Make it easy to join, harder to abuse
Once guest traffic is separated from the business network, the next step is to make access smooth while still controlled.
You have a few options.
Option 1: Simple shared password
- Use a dedicated guest Wi-Fi name and password
- Display the password at reception or share it verbally
- Change the password periodically, for example once a month
This suits small offices and clinics that want very low friction for visitors.
Option 2: Captive portal
A captive portal is the page that appears when you first join a network and try to browse. It may ask you to:
- Accept terms and conditions
- Enter a name, room number or email
- Enter a one time code given by reception
This suits cafes, coworking spaces, hotels and any place that wants a clear record that the user accepted usage terms.
You do not need to overcomplicate it. For an SMB, a basic portal that asks users to accept fair use terms is often enough.
Good identity hygiene for guests
Regardless of which option you choose:
- Avoid reusing the same Wi-Fi password for staff and guests
- Avoid printing the staff Wi-Fi details on the wall
- Do not give long term guest access keys to contractors who come once in a while. Consider short lived codes or passwords for them.
Principle 3: Control bandwidth and content
Even on an isolated guest network, you still want to protect your business and your internet connection.
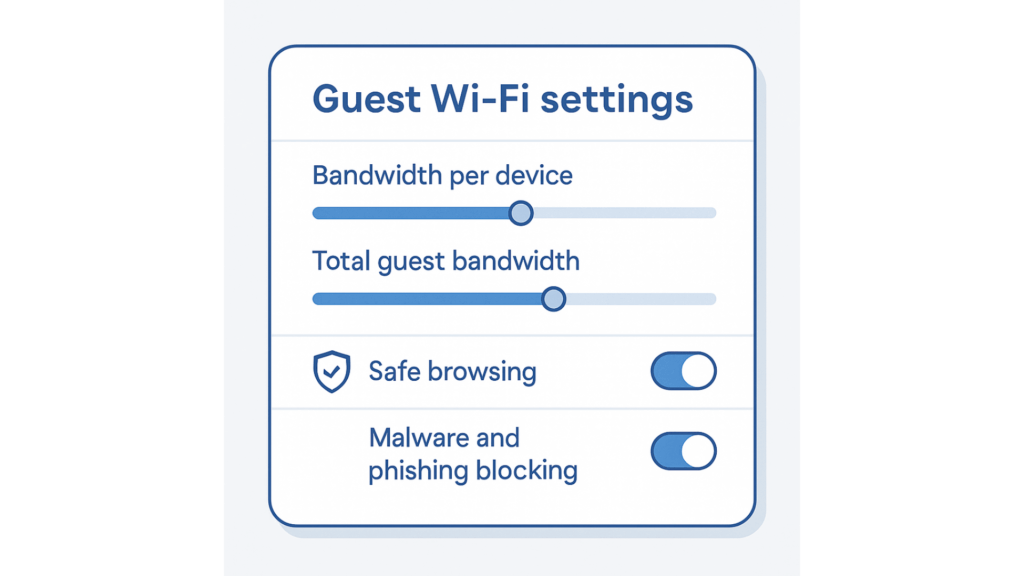
Limit how much bandwidth guests can use
This is usually configured as:
- A maximum speed per guest device, for example 5 or 10 Mbps
- A maximum total bandwidth for the guest network
The goal is not to punish visitors. It is to keep your core business traffic such as calls, payments and cloud tools running smoothly even if a few guests start heavy downloads.
Filter obviously risky destinations
You do not need to become a full time web censor, but some basic protections go a long way:
- Block access to known malware and phishing domains
- Optionally block adult or very risky categories if that fits your brand
- Log suspicious traffic patterns so your MSP can review them
This protects both your visitors and your reputation. A guest accidentally visiting a known phishing page on your Wi-Fi is still a bad look.
Do’s and don’ts of guest Wi-Fi for SMBs
Here is a simple checklist you can use with your IT partner.
Do
- Do create a separate guest SSID that is isolated from staff devices
- Do ensure the guest SSID cannot reach internal IP ranges or management interfaces
- Do enable client isolation so guests cannot see each other
- Do use a captive portal or simple password system that you can rotate
- Do apply basic content filtering and safe browsing protections
- Do limit guest bandwidth so the business stays fast and stable
- Do keep logs under your IT provider’s control for troubleshooting and legal protection
Do not
- Do not put guests on the same Wi-Fi as staff laptops and servers
- Do not expose internal printers, cameras or NAS boxes directly to guest networks
- Do not leave the same guest password in place for years
- Do not rely on home grade routers that treat guest networks as an afterthought
- Do not assume “we are small, no one would target us”. Many guest risks come from accidental infection, not targeted attacks.
How MSPs can turn guest Wi-Fi into a value add
For managed service providers, guest Wi-Fi is not just a checkbox. It is a visible, easy to explain value for clients.
You can:
- Offer a standard “secure guest Wi-Fi” package for all SMB customers
- Include segmentation, captive portal, bandwidth controls and basic filtering by default
- Brand the captive portal with the customer logo, so it looks professional
- Provide quarterly reports that show guest usage and blocked threats
- Use guest Wi-Fi as an entry point to a broader network hardening project
Most owners understand the risk as soon as you say “right now every visitor phone is sitting on the same network as your accounting PC”. You can then show how a simple change fixes that.
How Cybird keeps staff and guest access separated
With the right gear, secure guest Wi-Fi does not have to be a complex manual setup.
Cybird is designed for small and midsize businesses that want business grade Wi-Fi and security without enterprise complexity. On Cybird routers and cloud management:
- Staff and guest Wi-Fi are separate by design
- Guest SSIDs are mapped to isolated network segments that cannot see internal resources
- Peer to peer isolation stops guests from attacking one another
- Guest networks can have default bandwidth limits so business traffic stays fast
- Safe browsing policies apply to guests too, blocking known malicious and phishing domains
- MSPs can manage all of this centrally through the cloud, with simple checkboxes and templates
In many deployments, “Staff and Guest separation” is literally part of the initial setup. Choose which SSIDs are for staff, which are for guests, and the system applies the right isolation rules behind the scenes.
That means you can be generous with internet access without ever putting your internal data, point of sale systems or business applications at risk.
A simple plan to fix guest Wi-Fi in your office
If you are an SMB owner, here is a straightforward way to move from risky guest Wi-Fi to guest Wi-Fi done right.
- Ask your IT provider to review your current setup
- Are guests on the same SSID as staff
- Can a guest device reach internal IPs
- Introduce a dedicated guest SSID
- Name it clearly, for example “CompanyName Guest”
- Map it to a separate network or VLAN
- Apply isolation rules
- Block access from guest network to staff network
- Enable client isolation on the guest SSID
- Add a simple access method
- Choose between a shared guest password or a basic captive portal
- Make sure it is easy enough for reception staff to explain
- Set bandwidth and security policies
- Limit per device and total guest bandwidth
- Turn on malware and phishing protection for guest traffic
- Document and train
- Write a short one page guide for staff on how to give guests access
- Include who to call your MSP or internal IT if guests report issues
With a modern solution like Cybird, most of these items are handled through a friendly cloud dashboard. For many offices it is truly “just a few checkboxes” to go from risky to robust.

Founder & CEO of Cybird.