If you run a small business, “cybersecurity” can feel like a distant, technical concern.
But the thing that quietly hurts SMBs isn’t usually a dramatic Hollywood-style breach.
It’s the everyday business pain:
- a payment system going down during peak hour
- a client call dropping mid-negotiation
- a staff member clicking a risky link and losing half a day to cleanup
- unknown devices joining Wi-Fi and creating confusion
- repeated “Wi-Fi is slow again” moments that bleed productivity
That’s why cybersecurity posture matters. Not as jargon—but as a practical business outcome:
How reliably can your team sell, deliver, and get paid without disruptions?
What cybersecurity posture means in plain English
Cybersecurity posture is your business’s readiness across five basics:
- Prevention: reduce common threats before they enter
- Visibility: know what devices and activity exist on your network
- Control: manage access (staff vs guest, offboarding, accountability)
- Resilience: keep operating during outages, floods, or attacks
- Clarity: get insights without drowning in logs
The goal isn’t “perfect security.” The goal is fewer interruptions, lower risk, and faster recovery—so revenue doesn’t take random hits.
How better posture directly impacts revenue (real SMB scenarios)
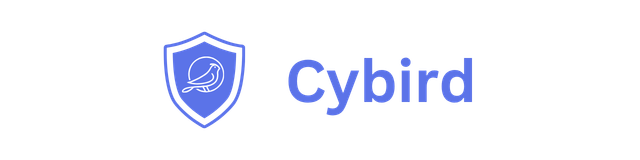
1) Uptime protects revenue continuity
Scenario: Your primary ISP goes down at 2 PM—right when your team is billing, calling customers, or using cloud tools.
Downtime is deadly for SMBs that depend on connectivity.
And it’s not just ISP outages—an infected PC or a misconfiguration can flood the local network and bring Wi-Fi down, and many small business routers simply crash under load.
Posture move that protects revenue:
- DoS protection + traffic management so the network can throttle excessive traffic instead of failing
- Automatic failover so “your work doesn’t have to stop” when the primary link fails
Business impact: fewer cancelled appointments, fewer failed transactions, fewer “we’ll do it tomorrow” delays.
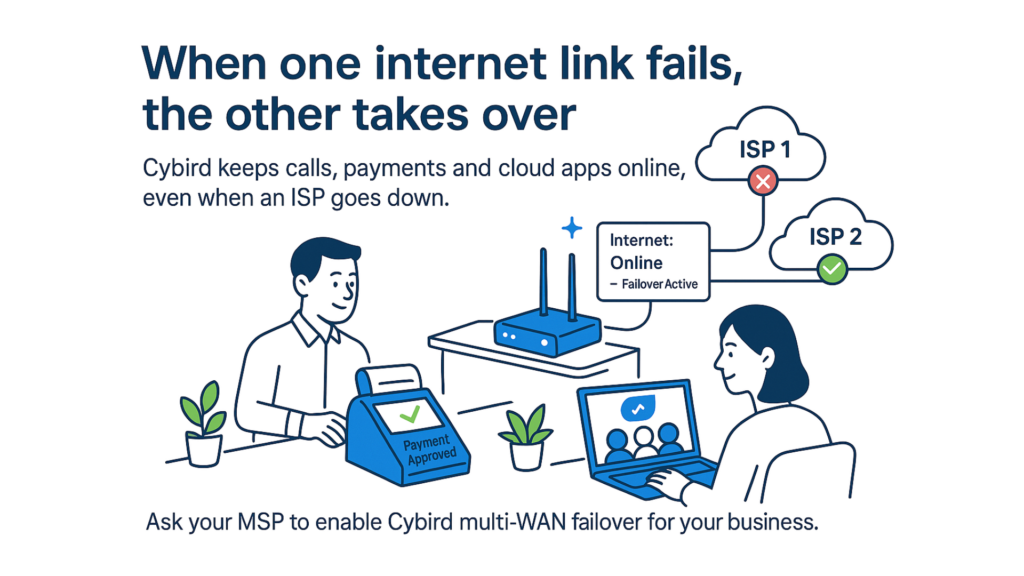
2) Smooth calls close deals
Scenario: A client call breaks up because someone is downloading a big file.
Without prioritization, the network treats all traffic equally—so a big download can choke bandwidth and ruin Zoom/Teams/VoIP quality.
Posture move that protects revenue:
Prioritize business-critical applications so voice/video gets bandwidth first.
Business impact: fewer reschedules, more confident demos, better customer experience.
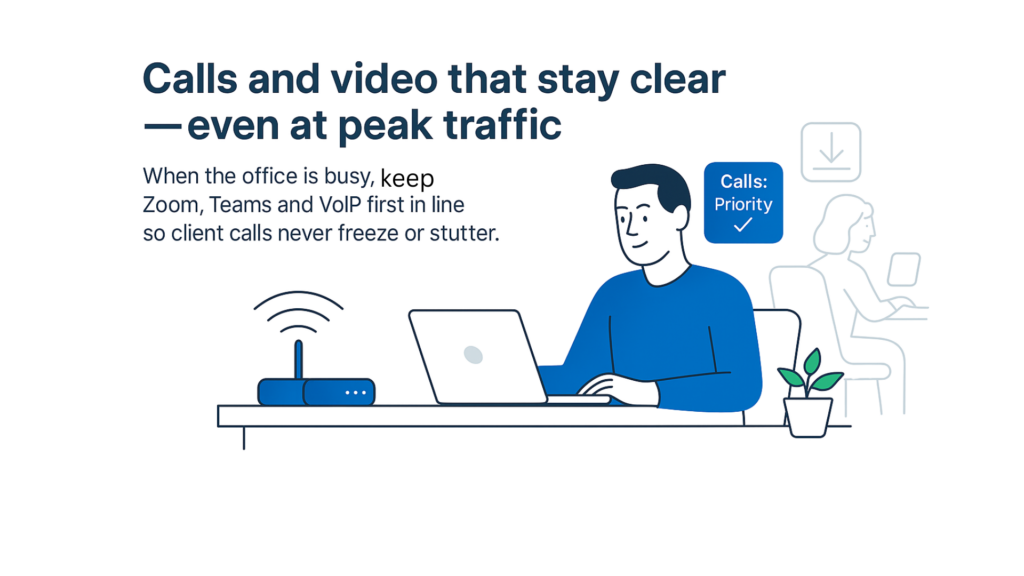
3) No shared passwords = fewer “mystery risks” and cleaner offboarding
Scenario: Everyone uses one Wi-Fi password—employees, guests, vendors… and sometimes ex-staff.
Shared passwords create “high risk, zero accountability.”
Per-user Wi-Fi credentials (WPA2-Enterprise) give each staff member their own login, making it easy to disable one person’s access and trace activity during incidents.
Business impact: fewer accidental exposures, smoother offboarding, less admin chaos when staff changes.
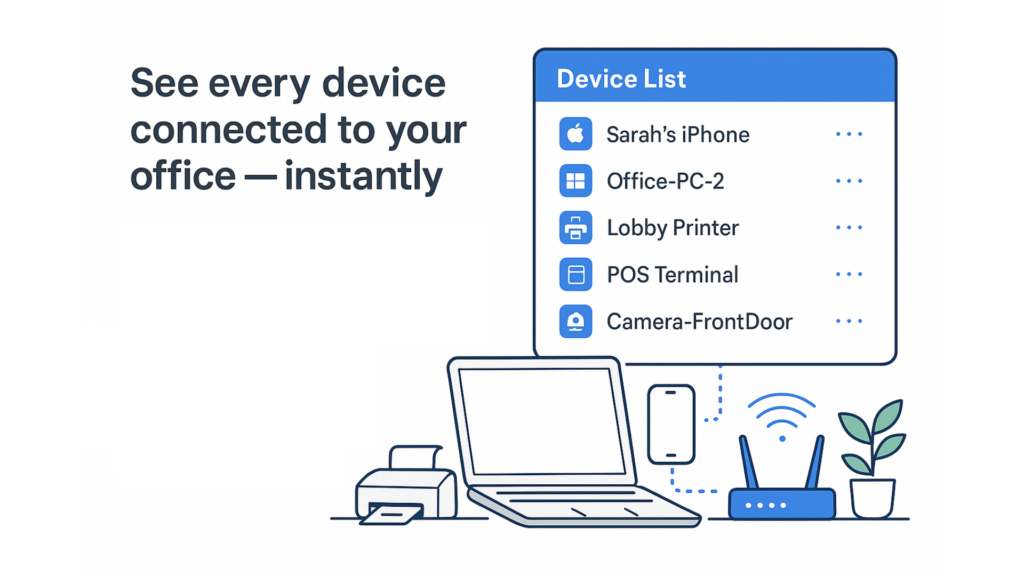
4) Visibility prevents “unknown device” surprises
Scenario: A new IoT gadget, camera, or personal device joins the network and nobody notices.
Many SMBs have a dozen+ devices connected and owners may be unaware when a rogue or risky device appears.
Device fingerprinting identifies devices by type, OS, and behavior—helping you discover unauthorized devices or even outdated devices with vulnerabilities.
Business impact: faster troubleshooting, fewer surprises, and less time wasted guessing “what is this device?”
5) Blocking malicious destinations reduces costly interruptions
Scenario: Someone clicks a sketchy download link or lands on a malicious website.
One wrong click can lead to infection. A practical posture move is blocking malicious sites & links before staff can click.
DNS-based filtering prevents access to known bad domains—stopping drive-by downloads and malware at the source.
Business impact: fewer cleanup days, fewer emergency IT calls, fewer “everything stopped” moments.

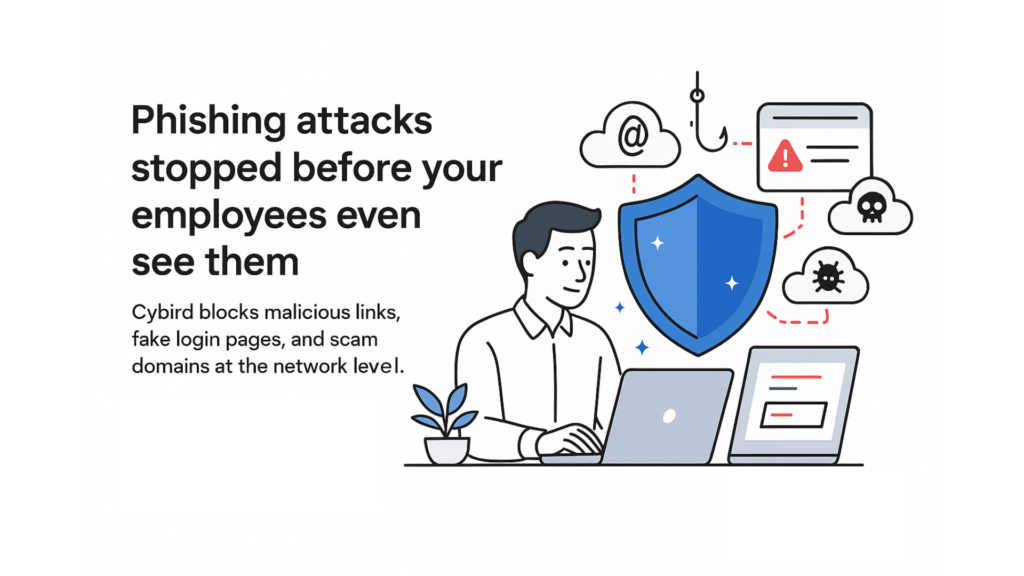
6) Phishing posture protects money, trust, and operations
Phishing remains a top entry point for incidents—and SMBs feel the impact fast because teams are lean. Your own topic notes phishing accounting for a large share of incidents and that human error is the biggest risk.
Posture move that protects revenue:
Combine training + technical safeguards, including blocking phishing links before they cause harm.
Business impact: less chance of credential leaks, fraud, ransomware downtime, and reputational damage.
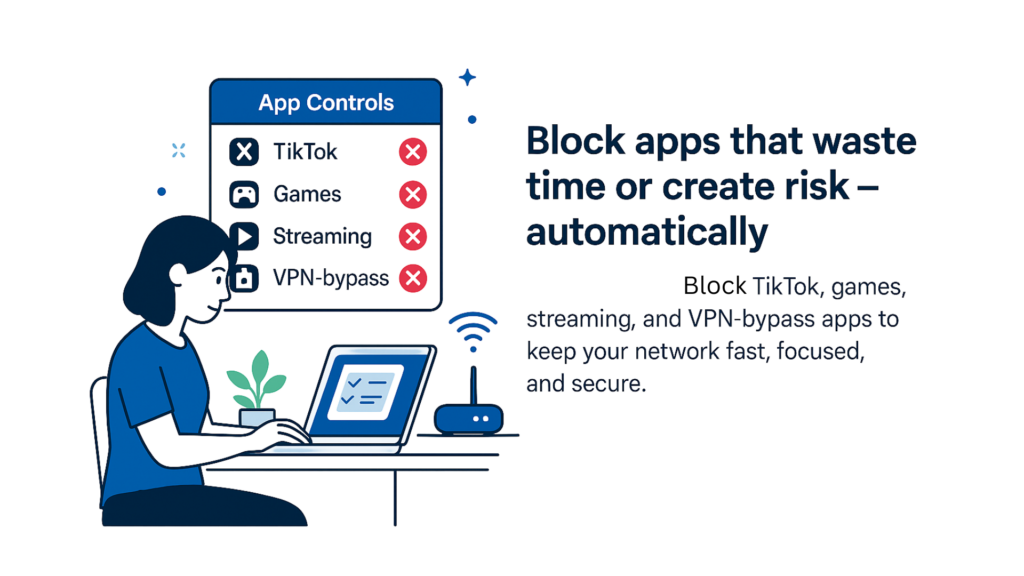
7) Productivity posture is also security posture
Unrestricted internet access can create both productivity loss and security risk.
Content filtering by category/time helps employees stay focused and reduces exposure to risky or inappropriate sites that can harbor malware.
Business impact: fewer distractions, less bandwidth waste, fewer risky browsing incidents.
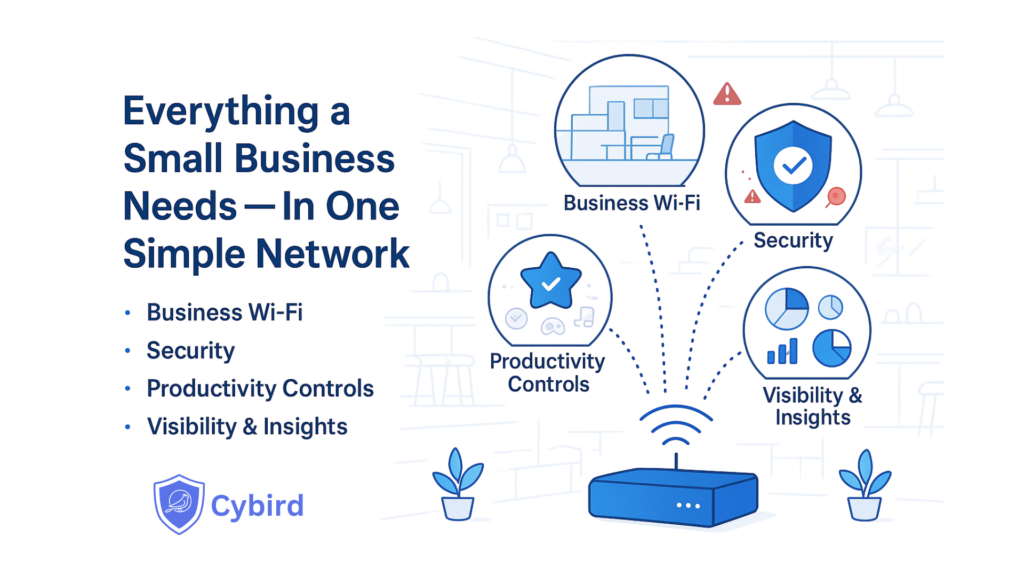
So where does Cybird fit?
Cybird is built for the SMB reality: you want enterprise-grade outcomes without needing a dedicated IT person. The content explicitly frames modern SMB security as simplified, low-touch, and attainable.
Cybird strengthens cybersecurity posture at the network layer—where every device connects—through practical controls:
1) Block malicious sites before they become incidents
Cybird uses DNS-layer protection to block known malicious destinations before users reach them.
2) Reduce phishing risk with real-time link blocking
Cybird’s “PhishDefender” is positioned as blocking phishing links in real time before they cause harm.
3) Know what’s on your network—automatically
Device fingerprinting provides visibility into device type/OS/behavior, helping SMBs spot anomalies and unknown devices without manual effort.
4) Stop shared Wi-Fi passwords and improve accountability
Per-user Wi-Fi credentials (WPA2-Enterprise) remove shared passwords and reduce insider risk; Cybird makes this simple and separates staff and guest access.
5) Keep calls and business apps stable
Application prioritization ensures business-critical apps get bandwidth first—helping protect customer experience and sales conversations.
6) Stay online through attacks and outages
Cybird’s posture includes DoS/traffic management so the network doesn’t crash under load, plus automatic failover to keep operations running.
7) Improve coverage and productivity with mesh Wi-Fi
Mesh networking eliminates dead zones with multiple nodes and a seamless single SSID, keeping teams connected and productive.
A simple ROI way to think about posture (SMB-friendly)
Instead of justifying security with fear, use business math:
Monthly impact = downtime avoided + IT/firefighting avoided + productivity protected + incident cleanup avoided
Even small improvements matter because they happen repeatedly—every week.

Founder & CEO of Cybird.