Most small business owners think cybersecurity means one thing: don’t get hacked.
So you buy antivirus, maybe add a firewall, remind people not to click suspicious links, and move on—because you have a business to run.
That’s completely reasonable.
But here’s the problem: the incidents that cost small businesses the most usually don’t start with something obvious. They start quietly, below the surface—like a slow leak in a pipe you can’t see—until one day you’re dealing with:
- a compromised email account
- missing money from a payment diversion scam
- customer data exposure
- downtime that stalls operations
- a “why can’t we log in?” crisis on a Monday morning
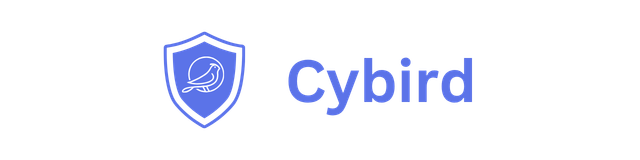
A simple way to understand this is the Iceberg model of cyber threats:
- Visible threats are above the water—easy to recognize.
- Hidden threats are below the water—quiet, ongoing, and often missed until damage is done.
This blog explains both sides in plain English, and then shows a practical way to protect your business without becoming a cybersecurity expert.
YouTube Presentation
Why small businesses are targeted (and why it feels unfair)
Attackers don’t only chase big enterprises. They also target small businesses because:
- Small businesses often have fewer controls (no dedicated IT/security team)
- They use the same tools as large companies (email, cloud apps, banking portals)
- They rely on uptime—even a few hours of disruption hurts
- Many attacks are automated, so criminals hit thousands of companies at once
The result: you don’t need to be “famous” to be a target. You just need to be online.
Part 1: The tip of the iceberg (visible threats)
These are the threats you can see and recognize.
1) Phishing emails (fake invoices, password resets, urgent requests)
This is the most common starting point.
What it looks like:
- “Your Microsoft password expires today”
- “Invoice attached — please review”
- “Document shared with you”
- “We need this wire transfer urgently”
Why it works: it targets people, not technology.
Business impact:
- stolen credentials
- email takeover
- vendor payment scams
- sensitive data exposure
SMB reality: even one person clicking once can be enough.
2) Malware from websites or downloads
Malware doesn’t always announce itself.
It can come from:
- a compromised website
- browser add-ons
- “free tools”
- fake PDF readers
- pirated software
Business impact:
- stolen passwords
- spyware
- slow devices and productivity loss
- a foothold for ransomware
3) Ransomware (the loud one)
Ransomware is what most people imagine when they think “cyberattack.”
But ransomware is often the final chapter, not the first.
Business impact:
- operations stop
- files become inaccessible
- customer work is delayed
- recovery costs spike
- reputation damage
Even if you don’t pay, downtime is costly.
4) Risky browsing (unsafe sites and categories)
Not every incident is a targeted attack. Sometimes it’s exposure:
- gambling/ad-heavy sites
- pirated downloads
- adult content
- “free streaming”
- sketchy plugins
These increase the chance of malware and compromise.

Part 2: The dangerous part of the iceberg (hidden threats)
This is where most small businesses are vulnerable—because these issues don’t look like “security problems” until it’s too late.
1) Password reuse and credential stuffing (silent break-ins)
Here’s how criminals break into accounts without “hacking” anything:
They take leaked password lists from old breaches and automatically try them on your:
- email accounts
- accounting platforms
- CRM tools
- vendor portals
- remote access tools
This is called credential stuffing.
Why it’s dangerous: it works when people reuse passwords.
Why it’s hidden: it looks like “normal login attempts” until someone’s locked out or money is moved.
The real cost: once email is compromised, attackers can reset passwords everywhere.
2) Email takeover and “quiet monitoring”
When attackers get email access, they often do something scary:
They don’t immediately attack.
They watch.
They set forwarding rules, monitor invoices, learn how your business pays vendors, then strike at the perfect moment with a payment diversion scam.
Business impact:
- vendor payment changes
- fake invoices that look real
- customers paying the wrong account
- reputational damage with partners
Why it’s hidden: your email still “works,” so nobody suspects a thing.
3) Rogue devices on your Wi-Fi (the unknown risk in most offices)
This is one of the most underestimated SMB risks.
Examples:
- an old printer with weak security
- a personal laptop used “just once”
- a contractor who joined and never left
- a cheap camera or IoT device
- a “temporary” Wi-Fi password shared widely
Why it matters: every device is a potential entry point.
Why it’s hidden: most SMBs don’t regularly check what’s connected.
4) Misconfigurations (small mistakes, big exposure)
Misconfigurations are one of the most common causes of security incidents.
Examples:
- guest Wi-Fi can access work devices
- everything is on one flat network
- weak Wi-Fi settings
- outdated router firmware
- “temporary exceptions” that become permanent
Why it’s hidden: nothing breaks… until an attacker finds it.
5) Shadow IT (tools adopted without approval)
Employees want to get things done. So they adopt tools:
- file sharing services
- remote desktop apps
- free SaaS trials
- browser VPN/proxy tools
This can lead to:
- data leakage
- compliance issues
- unknown access paths into the business
Why it’s hidden: it grows gradually, and nobody owns it.
6) Data exfiltration (slow leaks)
Not all incidents end in ransomware. Many are quiet data leaks:
- customer lists
- invoices
- HR files
- email archives
- internal documents
Why it’s hidden: operations continue while data quietly leaves.
7) Lateral movement (one device becomes many)
Attackers rarely stop at the first compromised device.
They move to:
- file shares
- NAS devices
- admin consoles
- other laptops
If everything can “talk to everything,” one mistake spreads fast.
Part 3: What practical SMB security looks like (without complexity)
Most SMB owners don’t want “more security tools.”
They want a setup that:
- prevents the most common attacks
- reduces impact when something goes wrong
- stays updated
- is easy to understand
- doesn’t require a security team
A practical approach includes:
A) Block malicious destinations before employees land there
Stopping access to known bad domains breaks many attacks early.
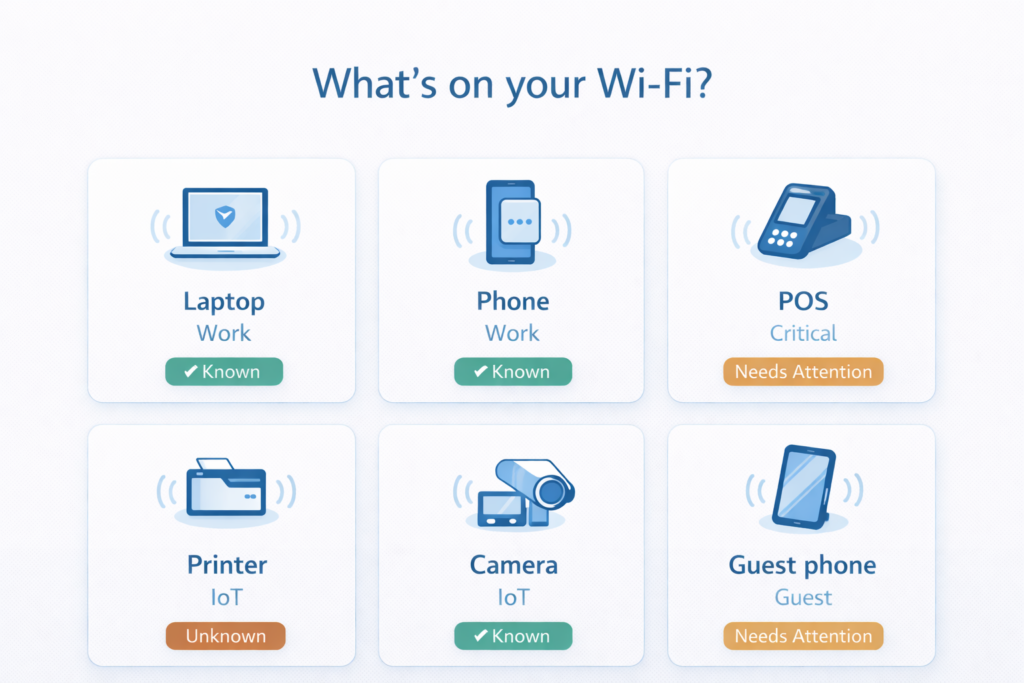
B) Know what devices are on your network (always)
If you can’t list all connected devices, you’re operating blind.
C) Separate devices into zones (segmentation)
At minimum:
- Work devices (laptops, phones)
- Guest devices (visitors)
- IoT devices (printers, cameras, smart TVs)
Segmentation reduces blast radius.
D) Reduce account takeover risk (identity hygiene)
This includes:
- MFA for email and key apps
- password manager
- removing old accounts quickly
E) Stay updated automatically
Outdated firmware is a silent liability.
F) Make security readable
You need “what changed?” and “what should I do?”—not raw logs.
Part 4: Where Cybird helps (and how it protects your iceberg)
Once you look at security through the iceberg lens, the role of a modern small-business network security platform becomes clear.
Cybird focuses on protecting the business at the network layer (your Wi-Fi + routing edge), where:
- every device connects
- most threats must “phone home” to work
- visibility is often missing in SMBs
1) Cybird helps stop visible threats early
Phishing and malicious links:
- Cybird can block access to malicious domains so users can’t reach the fake page.
Malware infrastructure:
- Many malware strains rely on contacting external servers. Blocking those destinations reduces impact.
Ransomware call-backs:
- Ransomware often needs outside communication for keys, commands, or exfiltration. Blocking known bad destinations helps disrupt the chain.
Unsafe web categories:
- Web filtering policies reduce exposure and improve productivity.
2) Cybird helps expose hidden threats SMBs usually miss
Device visibility & fingerprinting:
- Know what is connected (and detect unknown/rogue devices).
- This alone solves one of the biggest “below the iceberg” blind spots.
Device posture/risk signals:
- Identify which devices look risky or unmanaged so you can prioritize.
Profiles & policies:
- Separate guest/IoT/work devices and apply safer rules per group.
Anomaly visibility (depending on telemetry):
- Spot unusual behavior patterns that can indicate compromise or misuse.
3) Cybird helps keep protection current
Auto updates and centralized management help reduce the “we set it up once and forgot” problem that quietly increases risk over time.
A simple self-check for SMB owners
If you can’t confidently answer these, your iceberg risk is higher than you think:
- Do we know every device on our network today?
- Are guest and IoT devices isolated from work devices?
- Are phishing and malicious sites blocked network-wide?
- Are our router and network protections staying updated?
- Would we notice unusual behavior before it becomes a crisis?
Closing: The goal isn’t “perfect security.” It’s fewer bad weeks.
Small business security is not about becoming an expert.
It’s about reducing the chances of common attacks and limiting damage when something slips through.
The iceberg will always exist.
But with the right visibility, policies, and network protection, it becomes manageable—and your business stays focused on what matters: customers, revenue, and growth.

Founder & CEO of Cybird.