Build controls that reduce risk even when someone clicks.
Phishing isn’t a “user problem.” It’s a systems problem.
Modern phishing is designed to look routine: a vendor invoice, a shared file, a courier update, a “quick approval” from the boss, a KYC/GST notice, or a link that opens a familiar Microsoft/Google login screen. Attackers don’t need everyone to fall for it—just one person, once.
So the right question for SMBs in India isn’t: “How do I make my staff flawless?”
It’s: “How do I reduce damage when someone inevitably clicks?”
This blog lays out a practical, layered approach that combines identity controls, network/DNS blocking, segmentation, browser hygiene, and a reporting culture—without fear-mongering and without requiring enterprise complexity.
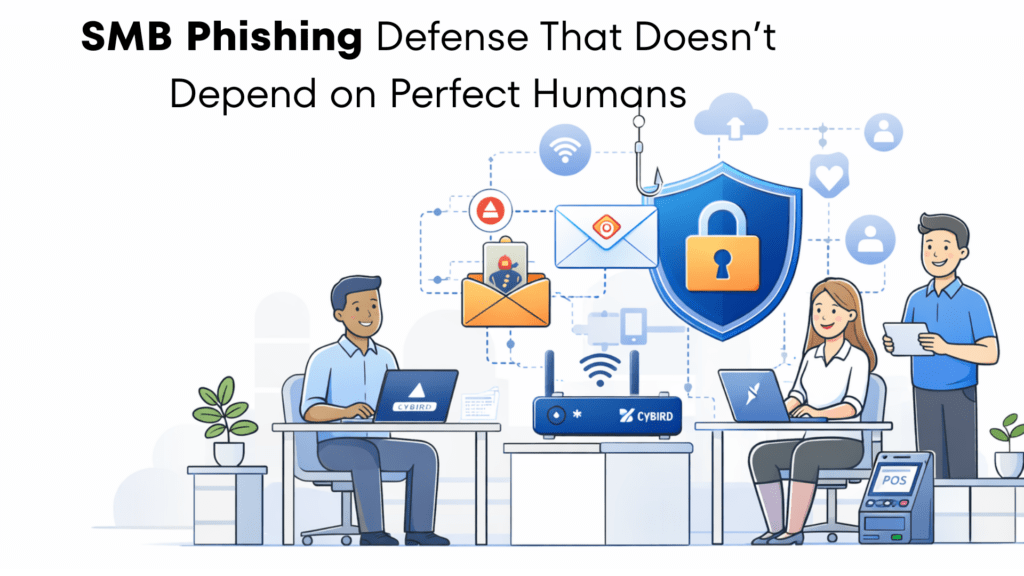
How phishing works today (the real chain)
Most phishing campaigns follow the same playbook:
- A message arrives (email, WhatsApp, SMS, LinkedIn).
- A link leads to a fake login page or “document download.”
- Credentials / OTPs / session tokens are captured—or malware is installed.
- The attacker abuses access (email takeover, invoice fraud, data exfiltration, lateral movement).
- The business pays—in money, time, reputation, or downtime.
Your goal is to break the chain at multiple points, so one click doesn’t become a company-wide incident.
Why SMBs in India are targeted (not because you’re “weak”)
Attackers optimize for ROI. SMBs often have:
- Fast payment workflows (vendor changes, urgent approvals, UPI/NEFT/RTGS)
- Mixed security maturity (some users have MFA, others don’t)
- Shared access patterns (shared mailboxes, shared Wi-Fi, shared devices)
- Many third-party relationships (CAs, logistics, agencies, SaaS tools)
You don’t need “perfect humans.” You need better defaults.
The layered controls that matter (and how they stop real attacks)
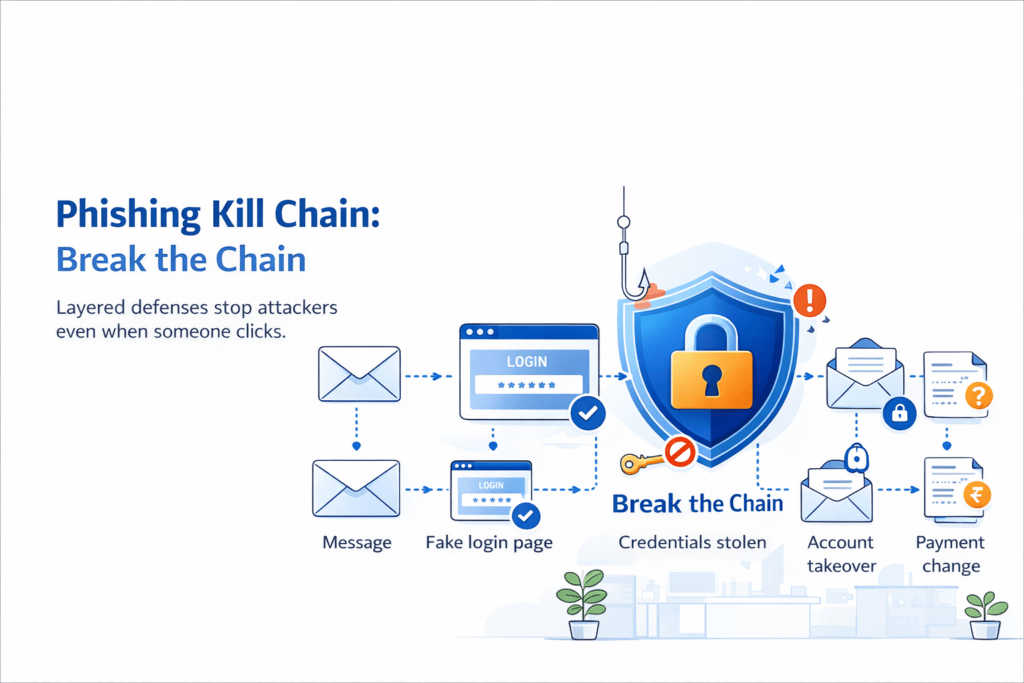
1) Identity: MFA + safer login rules
MFA is still one of the best “high leverage” controls—if implemented well.
What “good” looks like:
- MFA on email first, then finance, CRM, and admin portals
- Prefer authenticator apps / security keys where feasible
- Block suspicious logins (new device, unusual location) via conditional access
- Separate admin accounts from daily user accounts
What it prevents: many account takeovers even after password theft.
2) DNS / network blocking: stop risky destinations before the page loads
A huge amount of phishing depends on one thing: reaching a malicious domain. DNS and network-level controls can block:
- known phishing/malware sites
- suspicious newly registered domains
- risky categories commonly used in campaigns
What it prevents: the click from turning into credential theft or malware download—across all devices on the network.
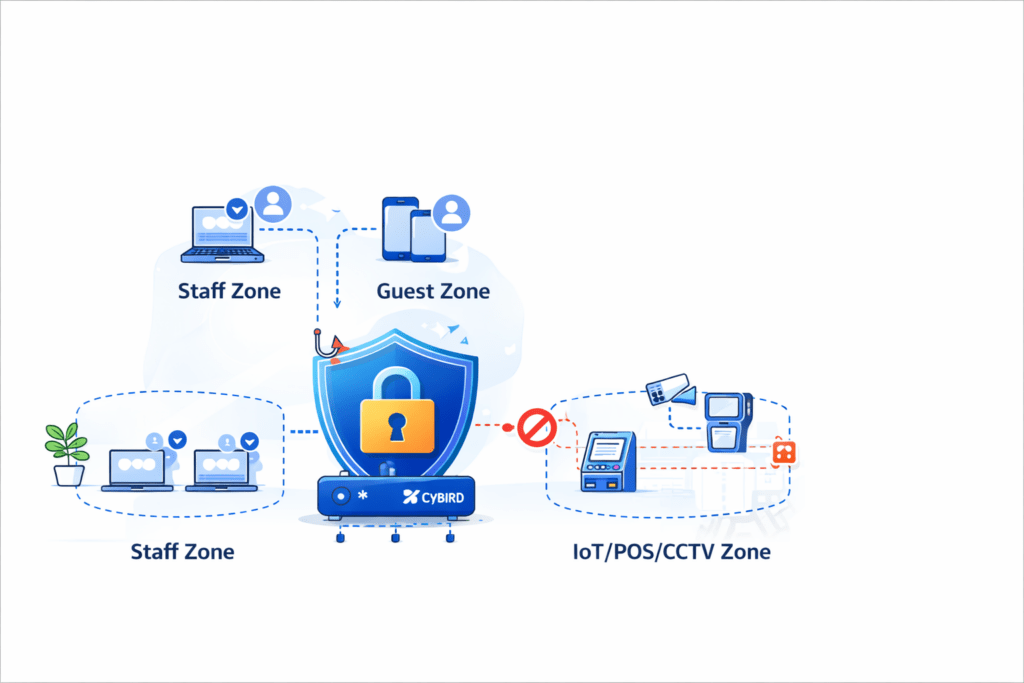
3) Segmentation: “one compromised device shouldn’t expose everything”
Flat networks are fragile. If a compromised laptop can talk to NAS, POS, CCTV, printers, and admin panels, attackers can move quickly.
A simple SMB model:
- Staff network (trusted)
- Guest network (isolated)
- IoT/POS/CCTV network (restricted)
- Admin interfaces reachable only from IT devices
What it prevents: lateral movement and “one click becomes many systems.”
4) Browser hygiene: small changes, big payoff
The browser is where phishing wins. Practical controls:
- Keep browser + OS updated
- Remove risky extensions; allow-list business extensions
- Enable phishing protection / safe browsing features
- Use a password manager to prevent reuse and reduce “typing passwords into random pages”
What it prevents: lookalike login pages, malicious downloads, and credential reuse.
5) Reporting + fast containment: turn incidents into “near-misses”
Training helps, but speed matters more:
- Make reporting easy (“Forward to IT” / one-click report)
- Don’t shame—reward early reporting
- Have a 15-minute triage habit: verify, reset, revoke sessions, check mailbox rules
What it prevents: a single compromised account spreading internally or becoming finance fraud.
Two SMB examples (how layers stop real-world outcomes)
Example A: Accounting team — vendor bank change fraud
Scenario: AP receives an email “from a vendor” claiming new bank details. Link opens a “document” that asks for Microsoft sign-in.
Without layers: credentials stolen → mailbox takeover → hidden forwarding rules → fraudulent payment instructions → money lost.
With layers:
- DNS/network blocking blocks the fake domain
- MFA stops the attacker from logging in
- Reporting triggers rapid containment
- Finance verification step catches the bank-change attempt
Result: a click becomes an alert—not a loss.
Example B: Sales team — fake shared file link
Scenario: A “lead” sends “RFP_Details.pdf” via a shared link. It’s a credential-harvesting page.
Without layers: account compromised → attacker phishes internally → finance/HR targeted next.
With layers:
- Browser hygiene blocks common lookalike patterns and risky downloads
- DNS/network blocking stops access to malicious destinations
- Conditional access flags abnormal login attempts
- Segmentation reduces blast radius if a device is compromised
Result: the attack fails to spread beyond the initial attempt.
A practical 10-point checklist (SMB-ready, no fluff)
If you want a “do this first” list:
- MFA on email + finance + admin portals
- Separate admin accounts from daily accounts
- Password manager for all staff
- DNS/network blocking for phishing/malware + risky categories
- Staff/Guest/IoT segmentation (at minimum)
- Guest isolation enforced
- Restrict admin panels to IT-only access
- Patch OS + browsers regularly
- Simple reporting channel + quick triage playbook
- Finance workflow verification for vendor/bank changes and urgent transfers
If you do only three things this quarter: MFA + DNS/network blocking + segmentation.
Free next step: get a quick security baseline
If you’re not sure where your gaps are, start with a quick baseline audit.
Cybird offers a free Small Business Security Audit designed to help identify vulnerabilities and strengthen defenses.

Founder & CEO of Cybird.